
Say the word “hacker,” and many people think of some sallow-skinned loner pounding out viral code in his grandmother’s basement. Social charms and computer hacking don’t go together – right?
Not so. In recent years, the escapades of well-known social engineering hackers have become better documented, and the image of hackers has morphed into a hybrid of the savvy and charismatic grifter of yore and the socially inept whiz kid from the basement.
What Are Social Engineering Hackers?

Cosmo, the Hacker ‘God’ Who Fell to Earth
Social engineering hackers are con artists. They manipulate people into doing certain things or divulging confidential information which they then use to enter corporate computer environments. Once in, they may steal personal and confidential information, defraud the person or business or shut down systems company-wide. According to Lifelock, thieves use a variety of old-school to next-generation techniques that give them access to sensitive data.
How Social Engineering Works
A friendly question like, “How’s the weather in your parts?” can yield the target’s city and state. With a name and location, a public records search can give an address and date of birth, information a social engineering hacker can use to obtain the target’s social security number.

How A Lying ‘Social Engineer’ Hacked Wal-Mart
Last year, a man going by the pseudonym Gary Darnell called a Canadian Wal-Mart, claiming to be a contract writer working on a multi-million dollar deal for the company. According CNN.com, within 10 minutes Darnell gained all sorts of confidential information from the manager, including payroll cycles, lunch break schedules and subcontractor names. Darnell directed the store manager to a virus-infected website under the guise of having him take an online survey, and when the computer’s threat-detection system blocked the site, the manager even called his IT representative and insisted the infected site be unblocked.
Social engineering hackers create an environment in which the target does all of the work. They send an email requesting a change in password information and let the recipient do all of the typing, or they assume the role of survey-taker and let the target answer the questions. A properly executed socially engineered hack has the mark divulge secure information without knowing its intended use until it’s too late. The request for information seems innocuous, until a professional puts it all together.
For a personal hack, a friendly question like, “How’s the weather in your parts?” can yield the target’s city and state. With a name and location, a public records search can give an address and date of birth, information a social engineering hacker can use to obtain the target’s social security number. This is often enough information to get credit card access or establish a new line of credit.
The Lure
Social Engineering Scene From “Hackers” (awesome classic geek movie on hackers, from 1995, still relevant!!)
In a recent article for Forbes, security expert Tomer Teller described “the lure” as the key to hacking the human mind. Equivalent to marketing’s “hook” or a salesman’s “pitch,” the lure is the mechanism that engages the target. It may be an announcement on Facebook or a well-crafted email that gets the person’s attention and requires an immediate response.
One of the more successful tricks for the business hack involves an email to employees requesting that they review their retirement plan. Companies sometimes do change retirement providers and financial planners do offer new retirement options, and it’s easy for hackers to set up a fake website using some official-sounding finance term and logo. Since the email does not contain an actual virus or overt spam language, it often gets by malware filters.
Once the lure catches its mark, from that point on the hacker is concerned about capturing “flags,” or sensitive pieces of data. The flags for this email scam are name, social security and financial goals.
Learn To Protect Yourself From a Social Engineering Hacker
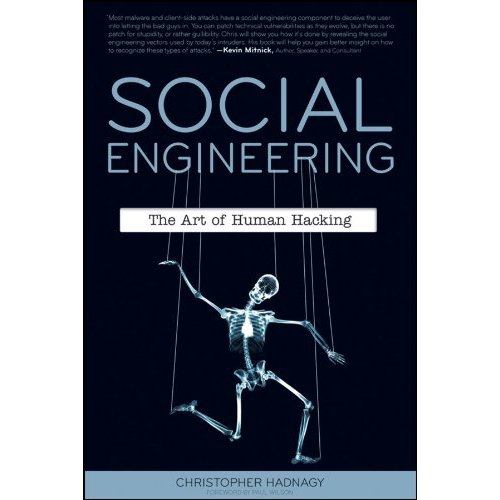
Social Engineering: The Art of Human Hacking
As the old adage goes, forewarned is forearmed. Social engineering hackers are, first and foremost, mental manipulators. They are relying on you being uneducated of the danger or afraid to say no to an authority figure. A good antivirus program can protect your computer, but the only way to defend yourself from your own humanity to be aware of the threat.
Lifehacker.com’s Melanie Pinola provides these tips to prevent becoming the victim of a social engineering hacker:
- The best way to keep yourself free from a scam is to stay clear of the scam artist. Knowing when you are a target is the first step. An identity theft protection company specializes in letting you know when one of your flags has been targeted. Once your data is looked at, the company notifies you so you can take action.
- Keep yourself informed. Sites like Snopes.com and Social-Engineer.org are devoted to letting you know when an email or social media post is false.
- Never give out your confidential information until you can verify the identity of the person asking for it. Any legitimate business should have no problem with this.
- Buy a shredder. Bank statements, credit card bills and receipts should be shredded to protect secure data.
- Use different logins for different services, make sure your passwords are strong and never use the same password twice.
- Use multi-factor authentication. This type of authentication requires the user to have two or more types of pieces of information, which makes it more difficult for hackers to get into an account even if they gain access to your username and password.
- Utilize the security question feature, but get creative; it’s often easy to guess or discover the answers to these questions. Develop your own code to ensure only you know the answers.
- Train your people. Whether it’s family or business, training is the key to protection. Teach your children about computer safety and have established policies and procedures for your employees.
Your Turn! Have you ever had an encounter with a “Social Engineer”? Have any tips we may have missed for avoiding being “hacked”? Let us know in the comments below! Thanks For Reading!




