The field of cybersecurity is growing rapidly, and there is a high demand for qualified professionals. In 2023, the global cybersecurity market is expected to be worth $223.9 billion, and
Top 5 Ways to Protect Your Businesses Mobile Devices
In the modern age, it’s incredibly important to have a watertight safeguarded IT infrastructure. Protecting your companies data from cybersecurity threats and ensuring that it’s fully compliant, it’s an invaluable
USB Flash Drives: Creative Ways of Utilizing Them
USB flash drives are often designed to offer exceptional performance and versatility. The capabilities go far beyond storing and transferring files. With the following tricks at your fingertips, you can
8 Ways To Secure Your Software
Virtually all businesses and organizations today use the internet and online platforms in one way or another. This has resulted in many amazing benefits such as efficient working environments, digital
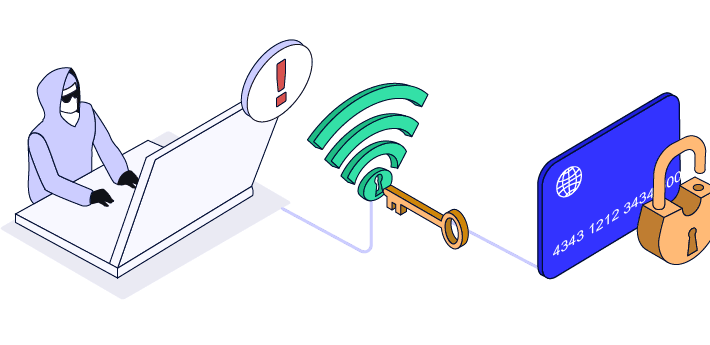
3 Reasons to Protect Your Online Data
In today’s world, unfortunately, your online data is never 100% secure. There will always be cybercriminals looking to hack your personal information and hold you to ransom over its safe
Fostering Network Security in a BYOD World
From the continuous escape from the 9-5 working schedules to the increase in technological advancements, it is almost impossible for businesses to ignore the need for BYOD policies. Slowly, employees
Keep your Computer from Slowing Down
It can be tempting to go out and buy a new computer when yours is not performing well. We live in a disposable culture. This is a waste of money,
The Dangers of the Dark Web
It’s not much of a secret that the dark web is a fairly unsavory place. After all, it typically appears in the news in connection to cyber crimes, narcotics arrests,