Ransomware has been in the news for a few years now, with everyone from individuals to large businesses suddenly discovering that their files have been encrypted — and they need to pay a ransom to regain access. Usually, stories about ransomware have been accompanied with advice to either pay the ransom, an expedient way to regain access, or how to remove the malware from the device and regain access via backups.

Think Your Business Is Safe? Think Again. 74% Of Businesses Become Victims Of Cyber Attack
However, that was before the WannaCry ransomware attack. Over the course of two days, the ransomware spread like wildfire, encrypting files on hundreds of thousands of machines in 150 companies, including those in medical centers and government. An anonymous hacker was able to identify a fatal flaw in the ransomware code, which effectively stopped the attack from spreading even further, but the incident did raise some important concerns about internet security — especially in relation to the Internet of Things.
Why WannaCry Was So Successful
Hackers Are Trying to Reignite WannaCry With Nonstop Botnet Attacks
According to security experts, 98 percent of the machines that were infected by the WannaCry ransomware were running Windows 7 or later — and had not installed a vital security patch that was issued in March 2017. Older editions of Windows operating systems and servers were also affected, and in the wake of the attack, Microsoft issued updates to those operating systems as well, despite no longer being supported.
The fact that so many computers were left unpatched, and still had vulnerabilities, highlights a key security concern with IoT devices: The need for them to be updated to avoid such large- scale attacks. Because IoT devices do not operate in isolation, if one becomes infected with malware, it can quickly spread to other devices on the same network and beyond. And if IoT devices are locked up by ransomware, the consequences can be devastating.
In fact, “Healthcare IT News” called the WannaCry attack and example of the “worst nightmare” in medical device security. Imagine what could happen if ransomware suddenly infects hundreds or even thousands of IoT medical devices, preventing them from working until the ransom is paid. Healthcare IT experts note that such a threat actually puts patients’ lives in danger, especially since it’s relatively easy for hackers to find out which medical devices are connected. For now, the most important step to mitigating potential attacks is to install patches, but WannaCry is serving as a wakeup call to IoT device designers that security cannot be an afterthought, and that as more devices go online, security methods need to be improved as well.
The Future of IoT Security
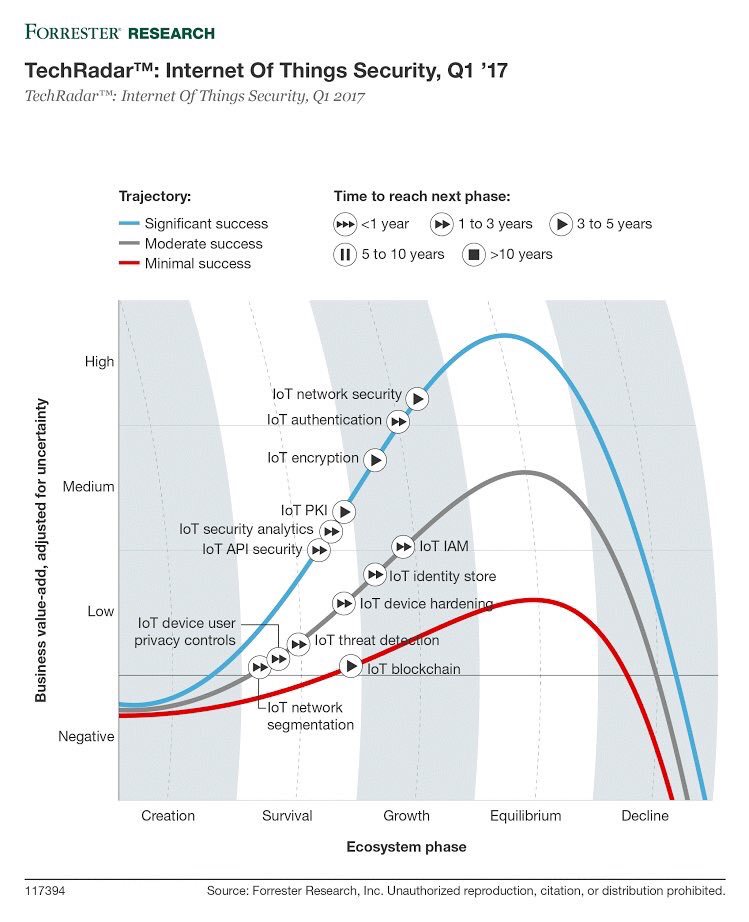
6 Hot Internet of Things (IoT) Security Technologies
Discussions about the security of the IoT are nothing new. However, the urgency has increased, and IoT vendors are looking at new ways to improve security.
For example, the idea that IoT devices cannot be updated or patched has become unacceptable, and vendors are looking at ways to mitigate that problem and ensure that all their devices can be updated, either automatically or manually. This includes identifying those devices, determining whether mitigation strategies can be put in place, and releasing updates as needed. In addition, for those devices that cannot be updated, it’s likely that they will no longer be updated, and the onus will be on users to determine whether to take the risk and continue using them, or invest in new devices that can be updated and secured.

Updates aren’t the only tactic that vendors plan to use to keep the IoT safe, though. Experts note that it’s not inconceivable for IoT devices to soon be equipped with more advanced encryption and authentication procedures for their 16-bit controllers, as well as licenses, improved endpoint security, artificial intelligence driven security, and other precautions. Still, these advances take time, and in the meantime, there is concern that another widespread attack could take place, and prove even more devastating.
We are still in the early days of the IoT, and learning more every day about what’s required to keep our connected world running. Incidents like WannaCry should serve as a reminder that connected devices, no matter how small or localized they may seem, are still computers connected to the internet, and thus still vulnerable to the dangers that more traditional machines have always faced.