If you have an e-commerce website, you need to identify Magecart as a massive security threat to your online assets. A recent analysis found that nearly 37% of websites have JavaScript vulnerabilities, and 80% of these websites are at risk of infiltration from malicious sources.
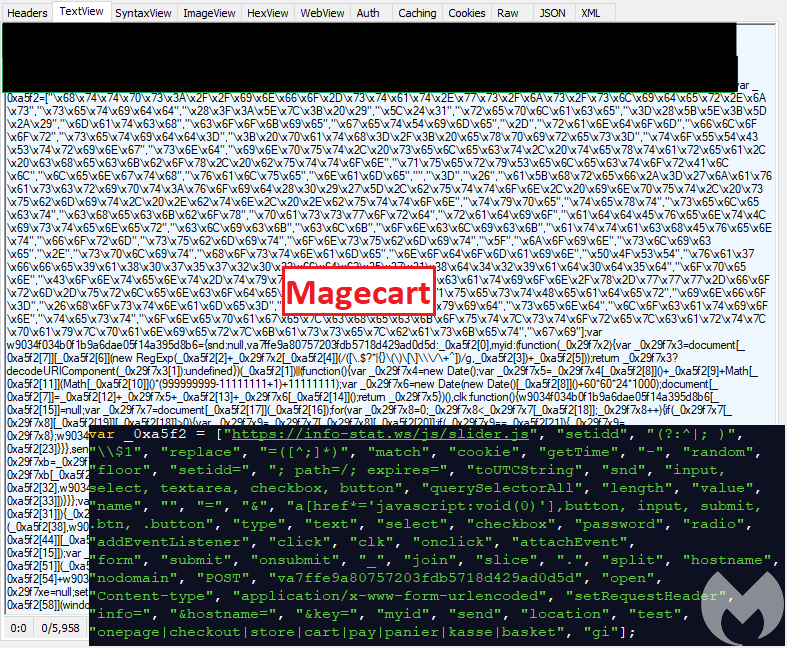
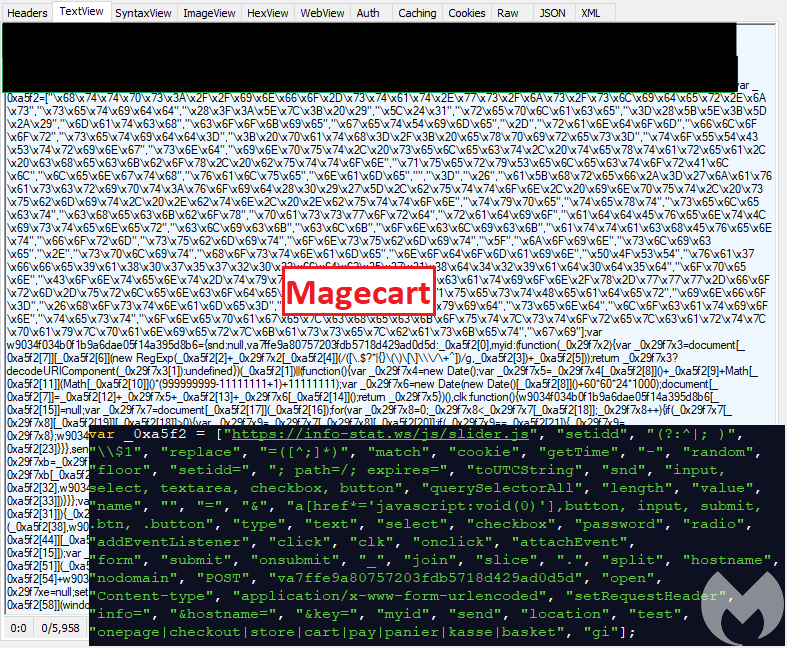
Many attacks take place through client-side browsers. Here, hackers inject a skimmer code on the third-party scripts to scrape sensitive information. Since the code is customized as per the first-party or third-party scripts, it can go unnoticed for weeks.
With the following mitigation techniques, you can avert threats like Magecart that fly under the radar of your online security.
Protection from the Third-Party Compromises

If you bought anything from these 19 companies recently, your data may have been stolen
After Magecart skimming, the website of Ticketmaster UK was hacked in 2018 through a third-party vendor chatbot. This shows the shift of hacking techniques from individual sites to third-party codes. As companies are adding more vendors to their e-commerce websites for allied services, this trend warrants more vulnerability.
To mitigate such risks, you can scrutinize the third-party scripts on your website. Identify the scripts having access to sensitive information and keep an eye on them. Also, conduct due diligence reviews of third-party vendor codes at regular intervals to control their security access levels.
Protection of the First-Party Codes
An updated and fine-tuned web infrastructure is more secure against Magecart attacks. You can use your web application firewall to protect the first-party codes from the hackers. Configure the firewall to alert and block the code injection attacks from malicious sources.
Also, set rules to block specific domains from accessing the information on your e-commerce website. These are traditional methods that may not suffice to protect against skimming codes.
Hence, you need a comprehensive approach to fine-tune not only the first-party code but also the third-party scripts.
Protection From Unauthorized Transfer of Personal Information
How to protect your data from Magecart and other e-commerce attacks
Magecart groups work stealthily to inject skimmer code into your first-party or third-party JavaScript. It can make your website extremely vulnerable to unauthorized transmission of customer data, especially personal information.
Hence, take proactive steps to control the situation before it blows out of proportion. Preventing the code from sending the data to a malicious domain is your safest bet. You can stop this unauthorized transmission if the codes are compromised. Implement a content security policy (CSP) to make this happen.
CSP helps you to mark the domains that can access your e-commerce store and the type of files they can transfer. With this procedure in place at the checkout phase, you can easily block scammers from sniffing credit card or other personal customer data.
Implementing and Managing CSP

Breaking Down Five 2018 Breaches — And What They Mean For Security In 2019
For implementation and management of content security policy, record the domains having access to your site, and approve the safer ones out of these.
You can also choose a website security platform that uses AI-based analytics to profile the website codes and scripts in real-time. It helps to automate the dynamic adjustments of web security policies to prevent any client-side cyber attacks that may cost you sensitive data.
So, protect your web assets with the right strategies and techniques. Choose a platform having the capability to prevent malicious attacks without costly incident response systems.




