Each brand new year brings lots of new and emerging cybersecurity threats. So, as 2018 is almost here, it’s time to look ahead to the coming year to see what
It’s Time To Go Into Security Overdrive!
You might not worry too much about security in your business but you should because the issue with security has never been higher and more apparent. Indeed, Global ransomware costs
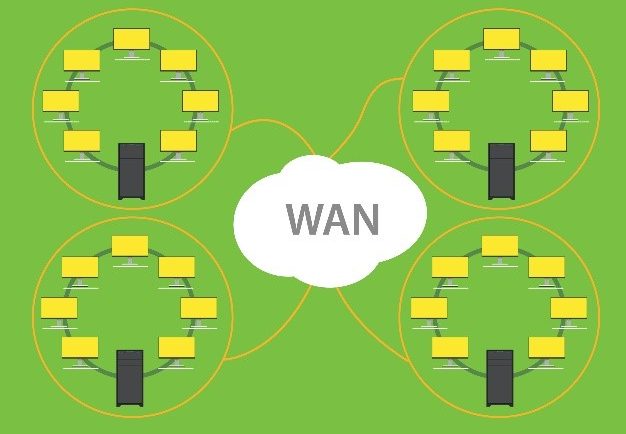
Why You Can’t Forget to Monitor Your WAN
Often, business environments devote resources to LAN network monitoring to reduce congestion and recognize failing components, both of which are significant obstacles for productivity and performance. Yet, while IT managers
How To Get Ahead Using Your Competitor’s Data
When it comes to creating an effective business strategy, there is one aspect that is all too often overlooked. Persuading potential customers to buy from your company over that of
SEO Misconceptions Debunked: Mistakes You Need to Avoid
Have you thought why SEO is pretty complex now? It`s due to the fact of Google using algorithm formula that can take a lot of factors while ranking any site.
Creative Writing as a Career: What Are Your Options?
Creative writing is a skill that opens up many different career opportunities. Writing is a skill that is required in many different fields, but creative writing is perhaps the easiest
The Underdogs Who Defied The Odds [Infographic]
Whenever you watch a movie, whether it be about love, war, or competition – do you ever find yourself rooting for the underdog? Of course you do, it’s because us
A World With Zero Latency
In a digital age, we expect to access information whenever we need it and quickly. This is especially important for businesses who aim to provide the best possible services for