For many New Jersey executives, technology is a paradox. It is supposed to drive efficiency and growth, yet it often feels like the anchor dragging the ship down. You sit
Small Business Security Solutions
Small businesses are increasingly the targets of sophisticated security threats, with reports indicating that 43% of cyber attacks are aimed at them. Yet, 60% of these small businesses lack the
Energy Companies Are Saving Millions Through MRO Data Normalization
MRO catalogs in energy companies often contain thousands of duplicate or inconsistent part records, driving procurement errors and excess stock. Recent adoption of structured MRO data practices gives procurement and
The Various Security Levels of Paper Shredders
Most people think all paper shredders work the same way—you feed documents in, and they come out destroyed. However, the reality is far more complex. Different types of sensitive information
Understanding the Role of Cloud Access Security Brokers in Modern Business
Modern businesses are moving more and more of their data into typical cloud-driven architectures. Managing and maintaining protocols in this new environment requires specialization. A CASB is a cloud-based software
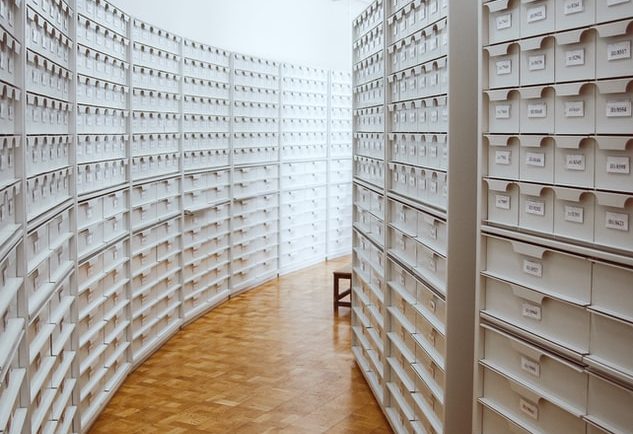
Choosing the Right VDR Provider A Comprehensive Guide for Secure and Efficient Data Room Management
The use of cloud storage for efficient data management is rapidly increasing in the global corporate sector. Studies revealed that almost 60% of all business world data is stored and
How to Prevent and Detect Business Identity Theft
Just like individuals can have their personal data stolen by criminals, so too can businesses have their identities stolen. Business identity theft involves a criminal impersonating a business, or an
The Benefits Of An Exemplary Data Room
The data room is an integral part of any merger or acquisition (M&A) process. It provides a secure, controlled environment for storing and distributing confidential documents and information related to