Most people think all paper shredders work the same way—you feed documents in, and they come out destroyed. However, the reality is far more complex. Different types of sensitive information
How to Verify Customer Information and Prevent Fraud
Any business must check whether customers are legitimate. Through an effective verification process, business owners can prevent fraudulent activities, detect fake identities, and comply with government regulations, especially when it
How to Prevent and Detect Business Identity Theft
Just like individuals can have their personal data stolen by criminals, so too can businesses have their identities stolen. Business identity theft involves a criminal impersonating a business, or an
What Are Identity Management Tools?
Identity access management (IAM) refers to the policies, procedures, and tools used by IT departments to manage digital identities and ensure that they have the appropriate level of access to
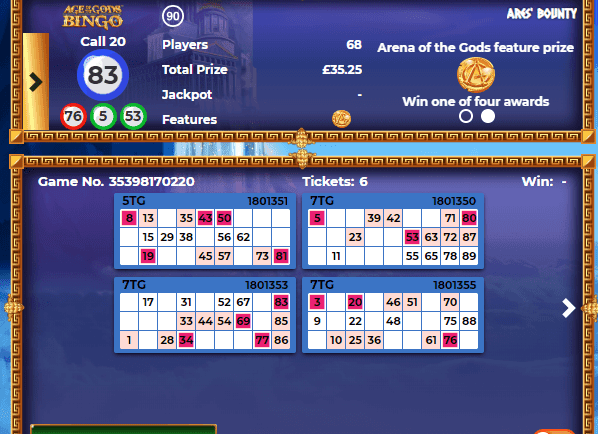
The Most Important Security Aspects of Playing Bingo Online
Online bingo has become extremely popular in the last few years, but what do you need to know about staying safe when playing in this way? The good news is
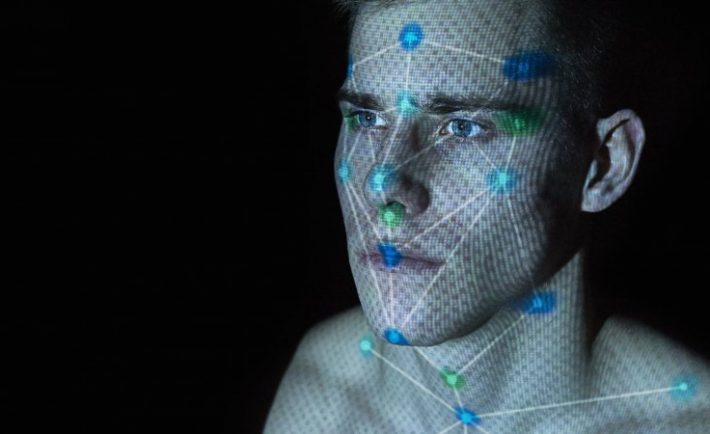
The Facial Scan Could Be a Problem in Online Businesses
Facial scan could be a problem in online businesses for a number of reasons. Privacy concerns: Facial scans collect a lot of personal data, including biometric information that can be used
Electronic Signature Security: Are Electronic Signatures Safe?
Electronic signatures, or digital signatures, are an easy way to organise your business digitally. By giving you the power to sign documents on screen, you avoid the hassle of printing,
3 Reasons to Protect Your Online Data
In today’s world, unfortunately, your online data is never 100% secure. There will always be cybercriminals looking to hack your personal information and hold you to ransom over its safe