
There are few businesses that aren’t making use of some sort of customer data nowadays. From simple sign-up forms to having their financial details on your records, it can be crucial to how you run your business. It can also help you gather insights that allow you to better market and deliver your services to their satisfaction and to your profit. However, if that sensitive data is misused or falls into the wrong hands, it can lead to a world of trouble on your end. For that reason, let’s make sure you’re both handling and protecting customer data as you should.
Consider what data you need to collect
How To Get Ahead Using Your Competitor’s Data
With some of the advantages of collecting data, especially in the retail industry, it can be hard to reel it back in and avoid collecting data that you don’t need. However, it’s important that you make sure that you’re not committing the sin of data saturation. This means collecting more data than you need. Not only can having too much information to parse make it harder to gain any useful insights, it just means that you have more data that hackers could potentially steal, meaning you get more risk with no benefit. If you notice that certain sets of data aren’t being used in any analytics, clear them and make sure they’re not collected in the future.
Be ethical and inform your customers about data collected
Data regulations are evolving, with the GDPR (which affects EU customers and any businesses involved with EU customers) being widely considered a harbinger of more changes to come. Effectively, staying compliant is all about ethical data collection. You have to make it clear to your customers what data you’re collecting, why you’re collecting it, how it will be used, and you have to inform them of any plans to share with third parties for any reason. Furthermore, your customers have to opt-in to share their data, it shouldn’t be slipped past them. Provide a clear and concise privacy policy for your website, or one that you can read out to them if you’re doing business over the phone or in person.
Use customer database software with security functions
How to Provide Cloud Data Security
While sometimes data can be lost, stolen, or altered as a result of malware and hackers breaking through your cybersecurity, it is often human error that is the cause of data-related mishaps. Using customer database software that reduces the ways in which its human editors can mess up can help you secure your data and make sure that it’s only used in the most appropriate ways. You can check that your customer relationship management software is GDPR compliant, for instance, and that it is secure on its end. Of course, there still needs to be some kind of training for your team to make sure they’re using that software in the most responsible manner possible.
Install what endpoint protection you need
Data – Where to Store it and Keep it Safe
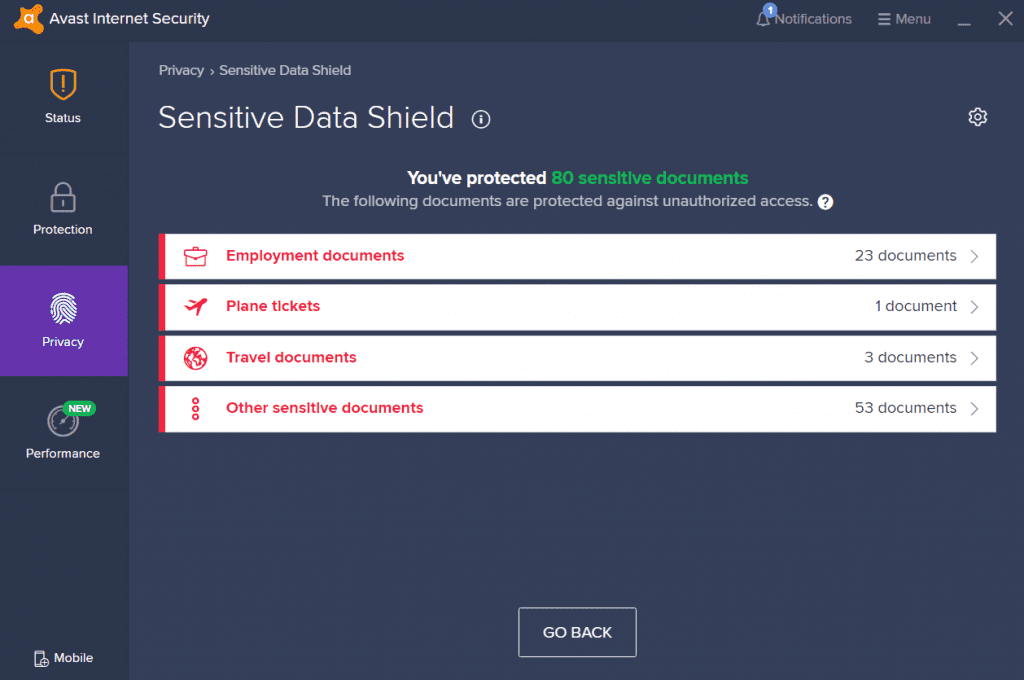
Aside from using database software that is secure, you need to make sure that you’re investing in the security your systems need as well. Effectively, the bigger and more complex your security scope, the more security you need to invest in. For any apps that transmit customer data, you need to ensure that end-to-end encryption is in place. For any devices that store or access that data, you need business anti-malware software. For any access points that your employees can use to get into the data, you need to make sure you have multi-step verification ensuring that they are the right people. Furthermore, you must have protection to filter out malware, spam, and other filetypes that could be potentially dangerous.
Teach your employees better network security
As mentioned, it is, unfortunately, the case that your employees open up a vulnerability in the system, not that hackers exploit existing vulnerabilities. It’s not always the reason, but it’s very likely to be the reason. You have to train your employees to be aware of cybersecurity. This includes teaching them about phishing scams and about not accepting any email attachments unless they verify and have good reason to trust the sender. Furthermore, if they use devices outside of the workplace, they should never use those devices in locations with public Wi-Fi. This includes semi-public wi-fi. For instance, taking their laptop to a cafe that provides the password out to all of their customers still means that anyone can learn and use that password to piggyback onto their hardware.
Make sure your systems are all up to date

Digital Defense: How To Protect A Data Center
You might think that keeping your anti-malware and security software up to date is enough, but it isn’t. From your device drivers to your operating system to your database software, and whatever other software you have and use on your systems, you have to make sure it is always updated. Out-of-date software and devices can lead to vulnerabilities that can be exploited. Most patches also contain security adjustments to get rid of those vulnerabilities so you have to keep up with them. This is also a good reason to make sure you’re not relying on legacy software that is no longer being updated. For instance, Windows 7 is no longer supported and thus will become increasingly more dangerous the longer you use it.
Track where the important data is and where it goes
As mentioned, you should be mindful of what data you ask your customers to provide you with. For one, not only can you risk losing valuable insights within a glut of irrelevant information, but you can also give yourself more of a burden when it comes to tracking that data. Invest time in data mapping so that, in the event of a breach or any other issue related to data, you can know what data you store, where you have it, and how it is used. This can help you quickly spot vulnerabilities, such as if you’re storing sensitive data on a device that is taken outside of the environment that you control. It can also help you secure your data better in the event of a breach.
Control who accesses your data

3 Reasons to Protect Your Online Data
Just as you should always be aware of what data you have and where you are keeping it, you should also be aware of who has access to that data. A lot of companies have a problem with allowing employees to access data that they don’t have any need to access. Furthermore, many companies fail to update their access settings, even after an employee leaves. In a major study, over half of all companies surveyed had over 1,000 sensitive files each that were open for every employee to access. Not only does this leave a business very open to the risk of a disgruntled employee misappropriating data. It means that if those employees are hacked, all the data they have access to is then open to the hackers.
Make sure you have a recovery process
Preventing your data falling into wrong hands should be your first priority. However, failing to act appropriately and to act fast in the event of a data breach can be an even worse mistake. If you collect customer data, data breach experts can help you craft a strategy on how to make sure you handle the eventuality that you are successfully targeted by hackers. For instance, the first thing to do is to have a means of detecting the breach and securing it, be isolating the affected systems and accounts as soon as possible, cutting off their access to more systems and data. From there, discovering what data was compromised and recovering any lost data is necessary.
Perform a full-scale security audit when you need to

Are Companies Doing Enough to Protect your Personal Data?
As part of your response to a data breach, you should investigate what vulnerabilities were exploited and close them. After all, in some cases, hackers will target companies they have already successfully targeted again, thinking they can double their bounty. Beyond that, you should run a comprehensive security audit that looks at all devices, tools, and accounts, and finds other potential vulnerabilities. It’s important to do this not only in the event of a breach or a near-miss but as a matter of routine. Taking the time to look for exploits and to close them offers the best chance of not being hit. Otherwise, you could be always reacting to threats instead of proactively protecting your business.
Inform who you need in the event of a breach
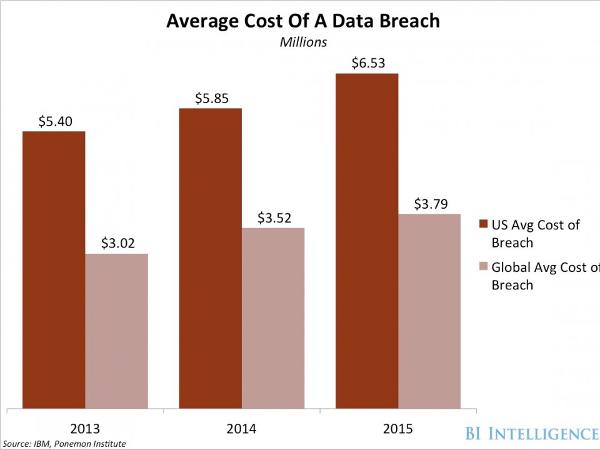
Impact of Data Breaches on Your Small Business
Lastly, if a data breach does happen, then you need to figure out who it affects and get in touch with them. Let them know the nature of the breach, what data was impacted, and when it happened. If you fail to inform those affected, be they customers, regulatory bodies, or third-party businesses, it can make you legally liable.
If you lose customer data, especially to a breach, the likelihood is that you won’t want more than two years. We mentioned steps to recover from such a disaster, but never forget that prevention is the best cure.








